As the dental industry continues to evolve, it’s crucial to stay ahead of the curve with modern techniques and technologies that enhance practice efficiency and patient experience.
Marketing Automation is a game-changing tool that every dental practice can leverage to maximize its growth potential.
Table of Contents
- What is Marketing Automation?
- What are the benefits of Marketing Automation?
- 6 Dental Marketing Automation Examples
- Automated Email Campaigns for Patient Communication
- Engage with Potential Patients Automatically
- Expand your online presence through automation
- Automated Patient Surveys and Feedback
- Personalized Patient Communication Strategy
- AI Assistants
- Find Out What to Automate
- Conclusion
What is Marketing Automation?
Think of marketing automation as a digital assistant—a powerful one. It takes care of the routine and time-consuming marketing tasks, but that’s not all. It’s a smart system that delivers personalized, relevant content to your patients and potential patients automatically, their engagement and connection with your practice.
Why Use Marketing Automation?
The advantages of incorporating Marketing Automation into your dental practice are plentiful:
Boost Patient Engagement: Foster stronger relationships with both existing and potential patients through consistent, timely, and relevant interactions.
Improve Customer Service and Personalize Patient Experience: Automating routine interactions enables more efficient service delivery and personalized patient experience.
Attract New Patients: Deploy targeted outreach efforts to engage potential patients effectively and encourage their conversion.
Save Time and Lower Costs: By automating routine tasks, you reduce operational expenses and free up your team to focus on what matters most – the care of your patients.
Increase Revenue: With targeted, smart, and efficient marketing, you can boost your dental practice’s profitability.
Gain a Competitive Edge: Stay a step ahead in the dental market by adopting progressive, automated marketing strategies.
6 Dental Marketing Automation Examples
- Automated Email Campaigns for Patient Communication
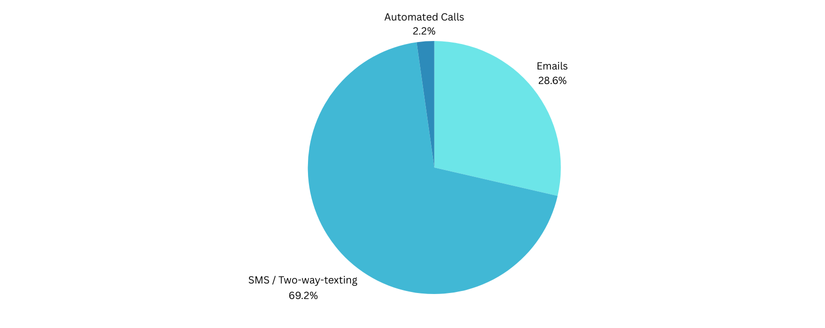
Email remains a powerful channel for patient communication. By employing automation, you can personalize each interaction, sending timely appointment reminders, tailored follow-up care instructions, enlightening newsletters, and educational content that specifically caters to individual patient needs. This method greatly enhances patient satisfaction and loyalty, keeping them connected to your practice.
- Engage With Prospective Patients Automatically
Turning potential patients into regular ones can be an exhaustive process. By implementing automated lead nurturing strategies, you can streamline this conversion process. Providing potential patients with relevant information and nudging them towards scheduling their first appointment can be the difference-maker in expanding your patient base.
- Expand Your Online Presence Through Automation
In this digital age, a positive online reputation can make a huge difference. Automation and AI solutions can help monitor and respond to online reviews and feedback across various platforms, ensuring you maintain an outstanding online presence and trust within your community.
- Automated Patient Surveys and Feedback
Continuous improvement and patient satisfaction go hand-in-hand. How do you achieve that? By listening to your patients. Automating patient surveys after their appointments, coupled with responsive action, can greatly enhance your service quality and patient experience.
A bonus: positive responses can trigger requests for online reviews, further bolstering your practice’s digital reputation.
- Personalized Patient Communication Strategy
Consider this: each patient comes to your practice with distinct needs and expectations. Just as the treatment approach varies for different dental conditions, communication with patients must be customized to resonate with their unique requirements and concerns.
For instance, consider two potential groups within your patient base: one group seeking routine dental cleanings, and another requiring oral surgery. These two groups have distinct expectations and require tailored messaging for effective engagement.
Through XLDent’s suite of automation services, customizing these communication strategies becomes not just possible, but seamless and efficient. Adopting automation in patient communication within your dental practice enhances operational efficiency, improves engagement, and ensures data accuracy.
Whereas manual methods can lead to errors or breakdowns in efficiency, automation offers instantaneous and error-free distribution of vital information. It permits personalized and timely responses, fostering improved patient satisfaction. This refined approach not only saves money, but time, which allows dental practices to focus more on patient care.
- AI Assistants
AI-driven chatbots can instantly — and accurately — respond to patient inquiries. This use of advanced technology not only caters to the modern patient’s preference for quick responses but also reduces the workload on your staff, allowing them to focus on other critical areas.
Innovation and modernity, coupled with a dedication to offering the best patient experience, are the cornerstones upon which XLDent stands. Using automation in your practice is not just an evolutionary step — it’s a strategy to set your practice apart and enhance your delivery of patient care.




 Subscribe
Subscribe Subscribe
Subscribe



